.svg)

AI-Driven Cyber Incident Response Platform
AiiR orchestrates the entire breach lifecycle—from detection and investigation to negotiation, compliance, and recovery.

Why AiiR Changes Breach Response
AiiR helps organizations respond faster, reduce financial impact, and maintain compliance during cyber crises.

Platform Features
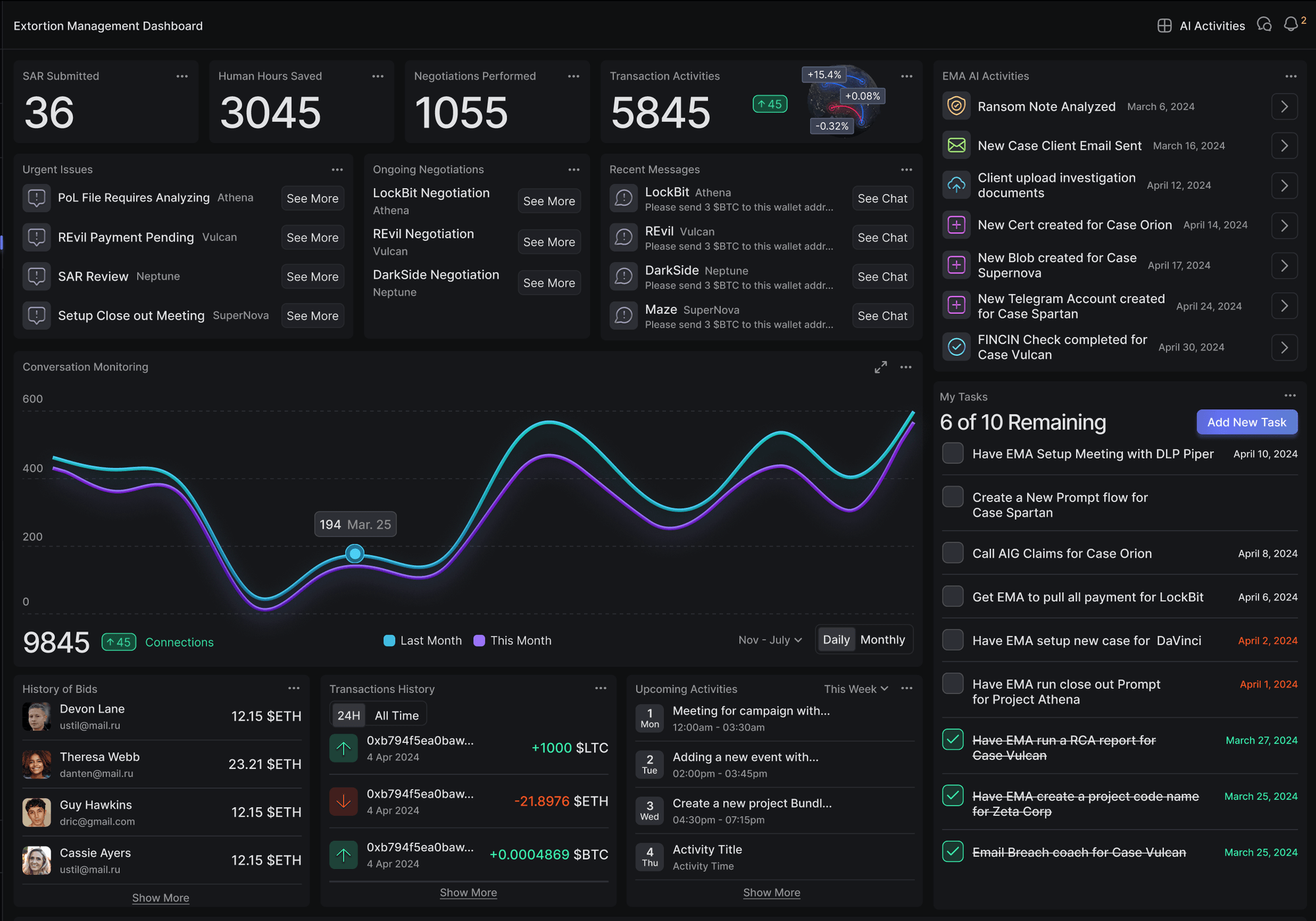
AI-Guided Ransom Negotiation
Leverage CEIRA — AiiR’s continuously learning AI agent trained on threat actor behavior, negotiation psychology, and OFAC compliance patterns.The platform provides intelligent negotiation strategies, financial analysis, and response guidance to minimize ransom exposure
Key Capabilities
• AI negotiation strategy
• Threat actor intelligence
• Ransom payment analysis
• Negotiation timeline tracking
• Evidence preservation.
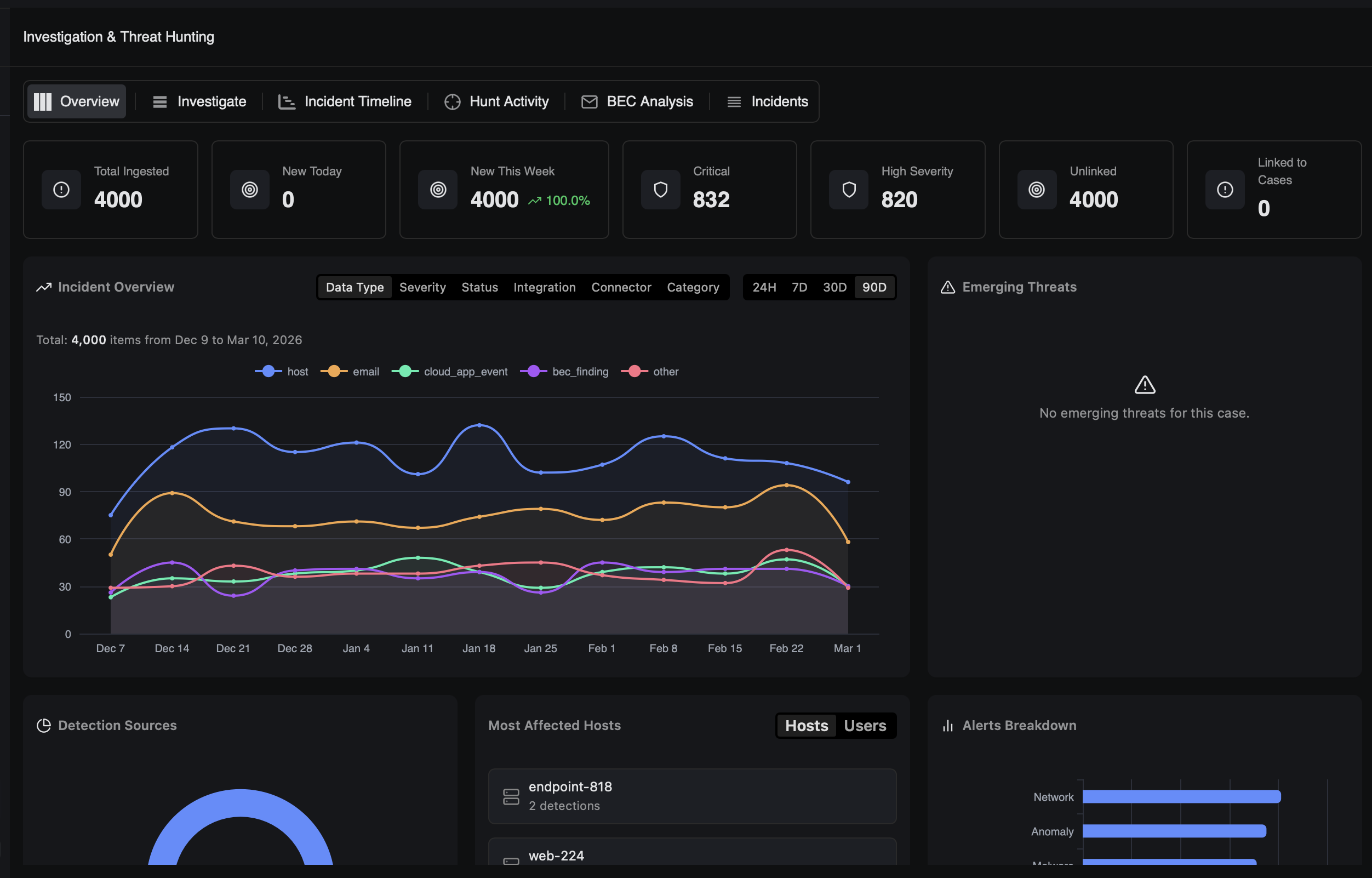
AI-Driven Investigation & Threat Hunting
AiiR correlates forensic evidence, threat intelligence, and incident telemetry to accelerate investigations and identify attacker behavior.
Capabilities:
• IOC correlation
• Threat actor mapping
• Evidence timeline
• Automated investigation playbooks
• MITRE ATT&CK alignment
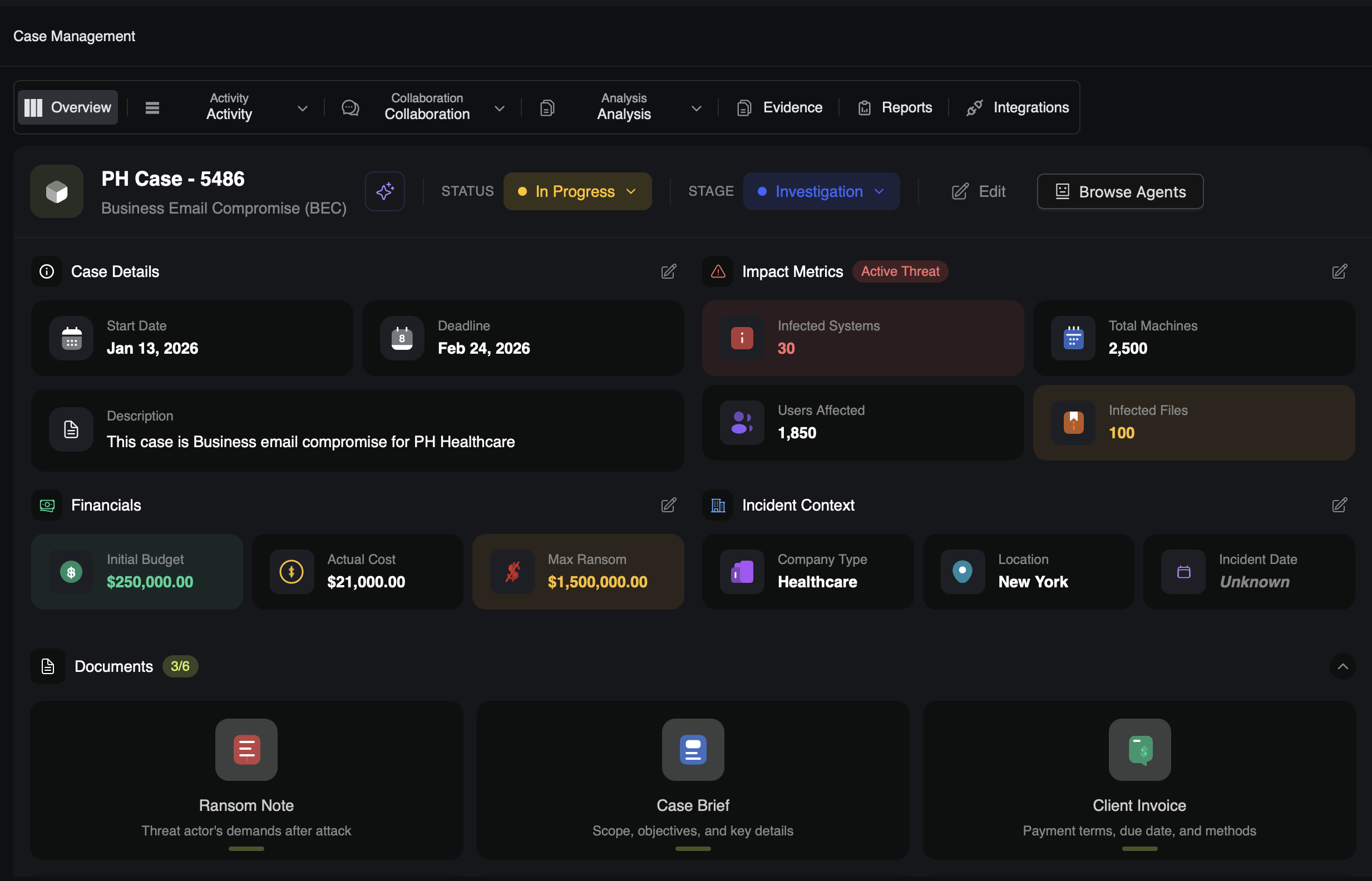
Incident Command Center
Centralize incident coordination, case management, and response workflows in a single operational command interface.
Capabilities:
• Case management
• Response task orchestration
• Responder coordination
• Incident timeline
• Communication tracking
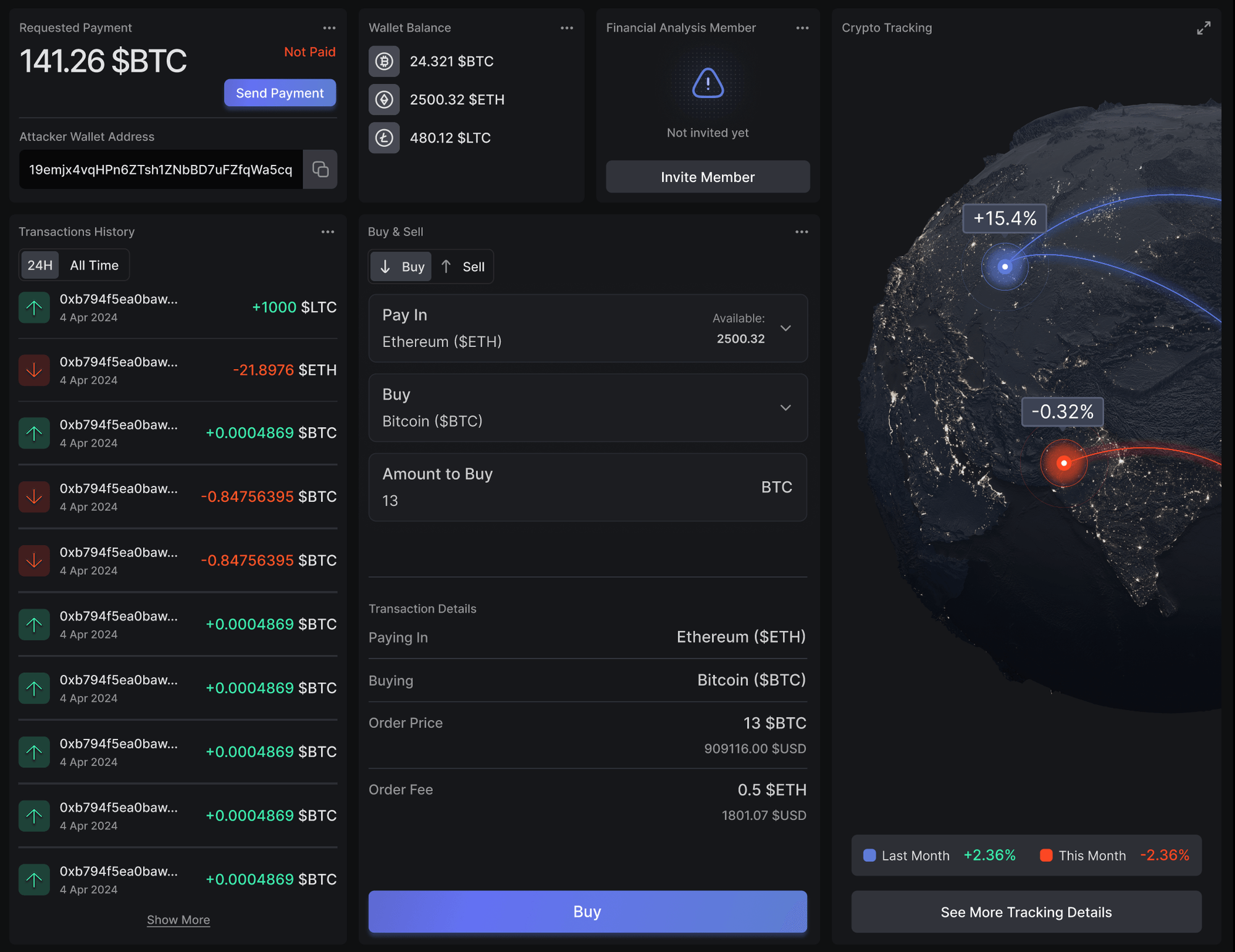
Secure Crypto Payment Orchestration
Manage ransom transactions securely with integrated wallet management, payment tracking, and financial audit trails.
Capabilities:
• Wallet management
• Transaction Monitoring
• Payment Approvals
• Blockchain Tracing
• Financial Audit Logs
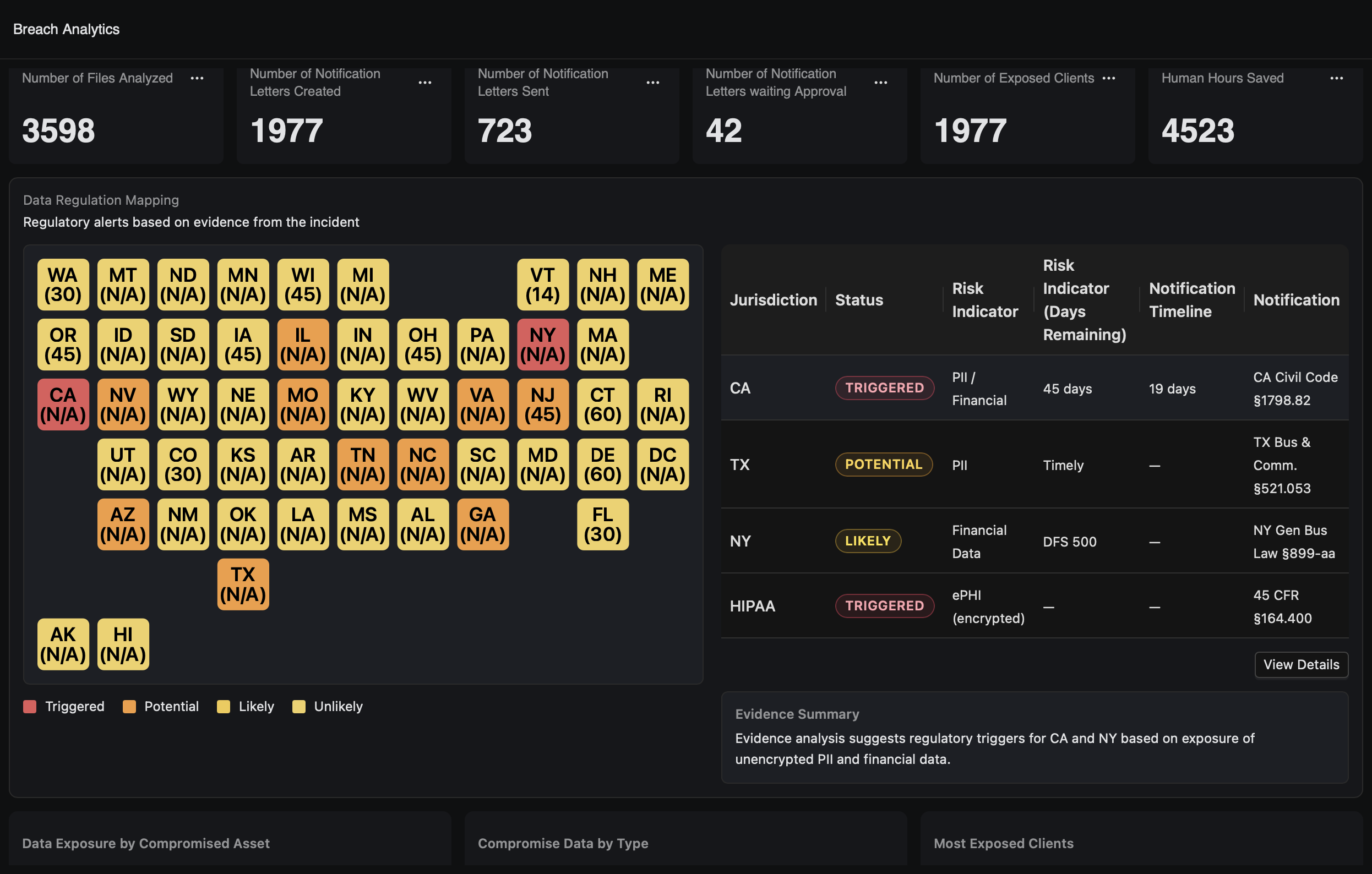
Automated Compliance & Legal Reporting
Automatically generate structured incident documentation and compliance reports for regulators, insurers, and legal teams.Centralize incident coordination, case management, and response workflows in a single operational command interface.
Capabilities:
• Breach notification tracking
• Regulatory reporting
• Evidence chain-of-custody
• OFAC compliance checks
• Litigation-ready documentation
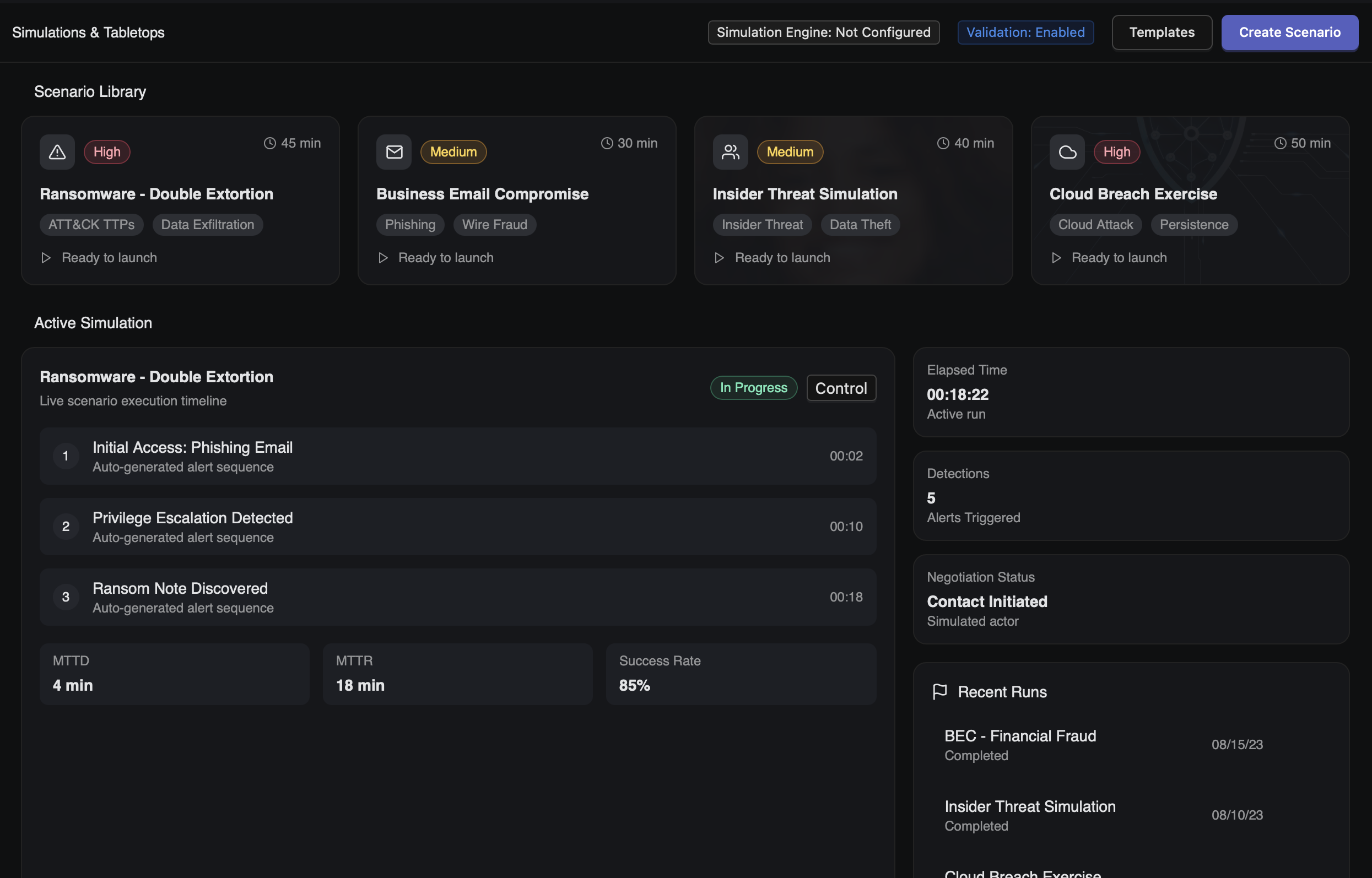
Simulation & Tabletop Exercises
Prepare organizations for cyber crises with simulated breach scenarios and response training exercises.Manage ransom transactions securely with integrated wallet management, payment tracking, and financial audit trails.
Capabilities:
• Breach simulations
• Tabletop exercises
• Response readiness scoring
• Training analytics
• Scenario replay
Unified Security Control Fabric
Integrate security tools, threat intelligence feeds, and incident data into a unified response platform.Automatically generate structured incident documentation and compliance reports for regulators, insurers, and legal teams.Centralize incident coordination, case management, and response workflows in a single operational command interface.
Capabilities:
• Tool integrations
• Telemetry ingestion
• Automation triggers
• AI orchestration• platform APIs


.svg)