News

Dark Web Leak Sites and Extortion: What You Need to Know

.
February 10, 2026
Educational
Phases of a Ransom Negotiation: A Psychological and Tactical Breakdown

.
February 10, 2026
Educational

The AI Arms Race: How Threat Actors Use AI—and How AiiR Fights Back

.
February 10, 2026
Educational
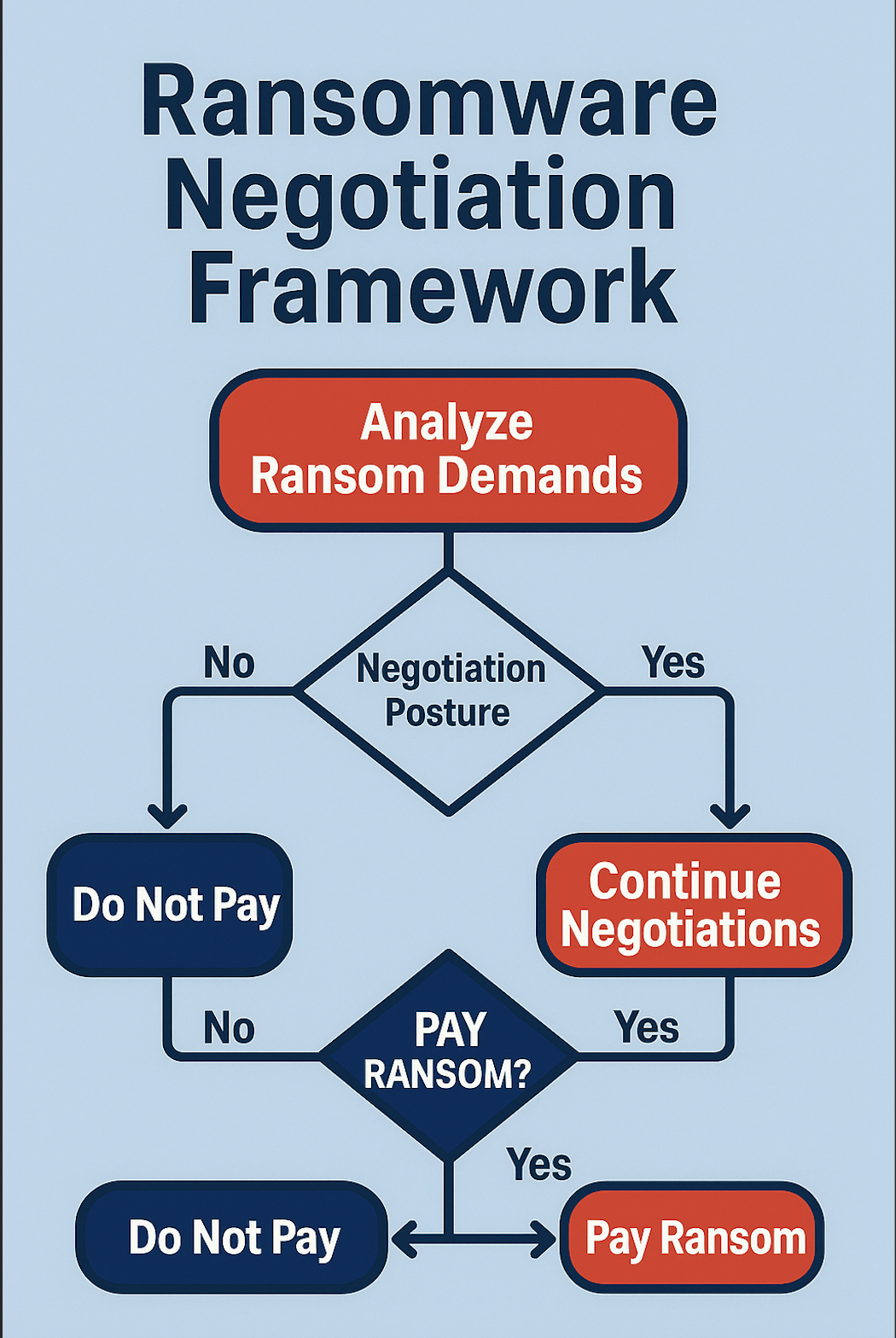
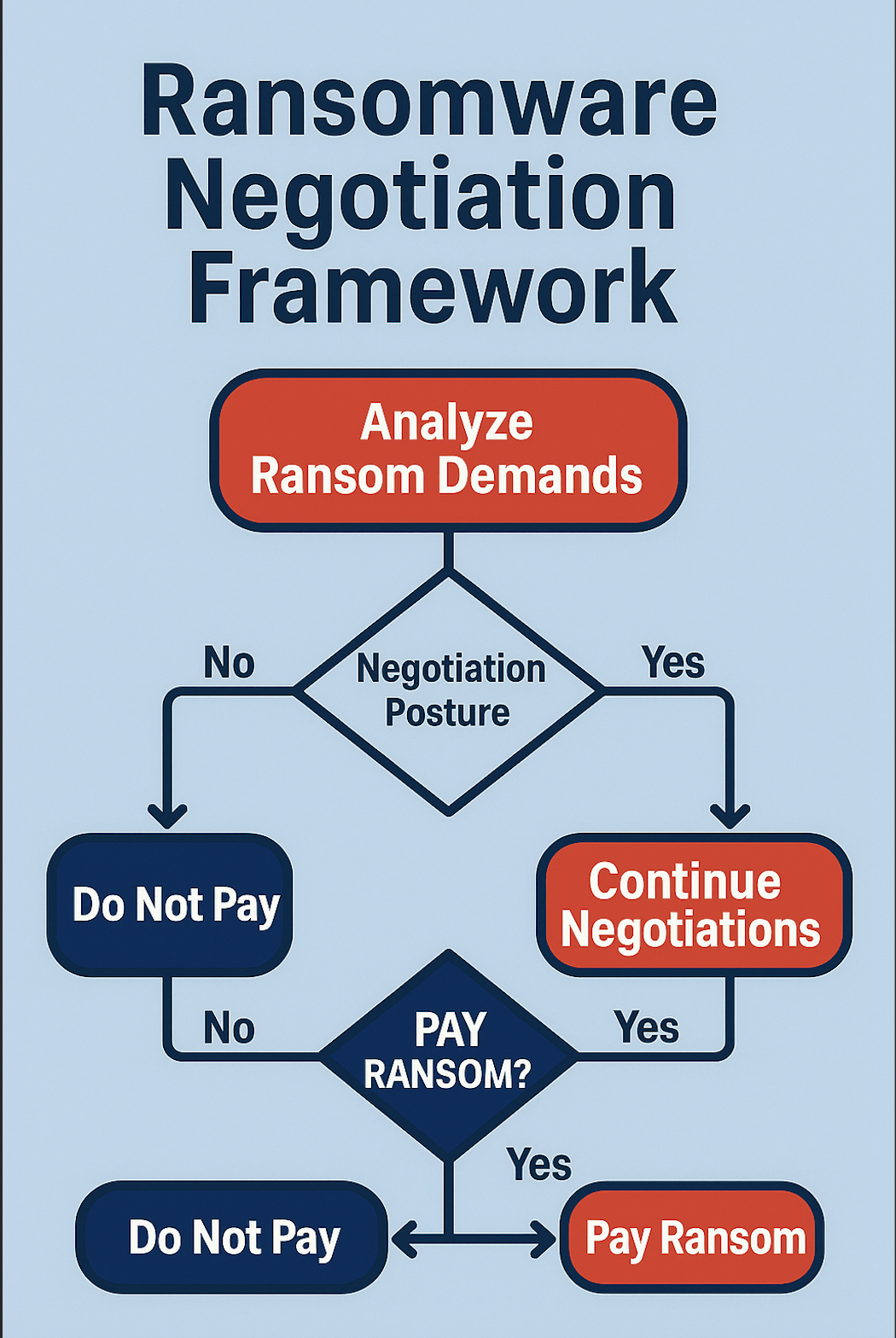
How to Evaluate and Compare Ransomware Negotiation Frameworks

.
February 10, 2026
Educational

Crypto Tracing in the Shadows: How Blockchain Forensics Guides Negotiation

.
February 10, 2026
Product
Running Effective Ransomware Tabletop Exercises—Now Transformed by AiiR

.
February 10, 2026
Educational
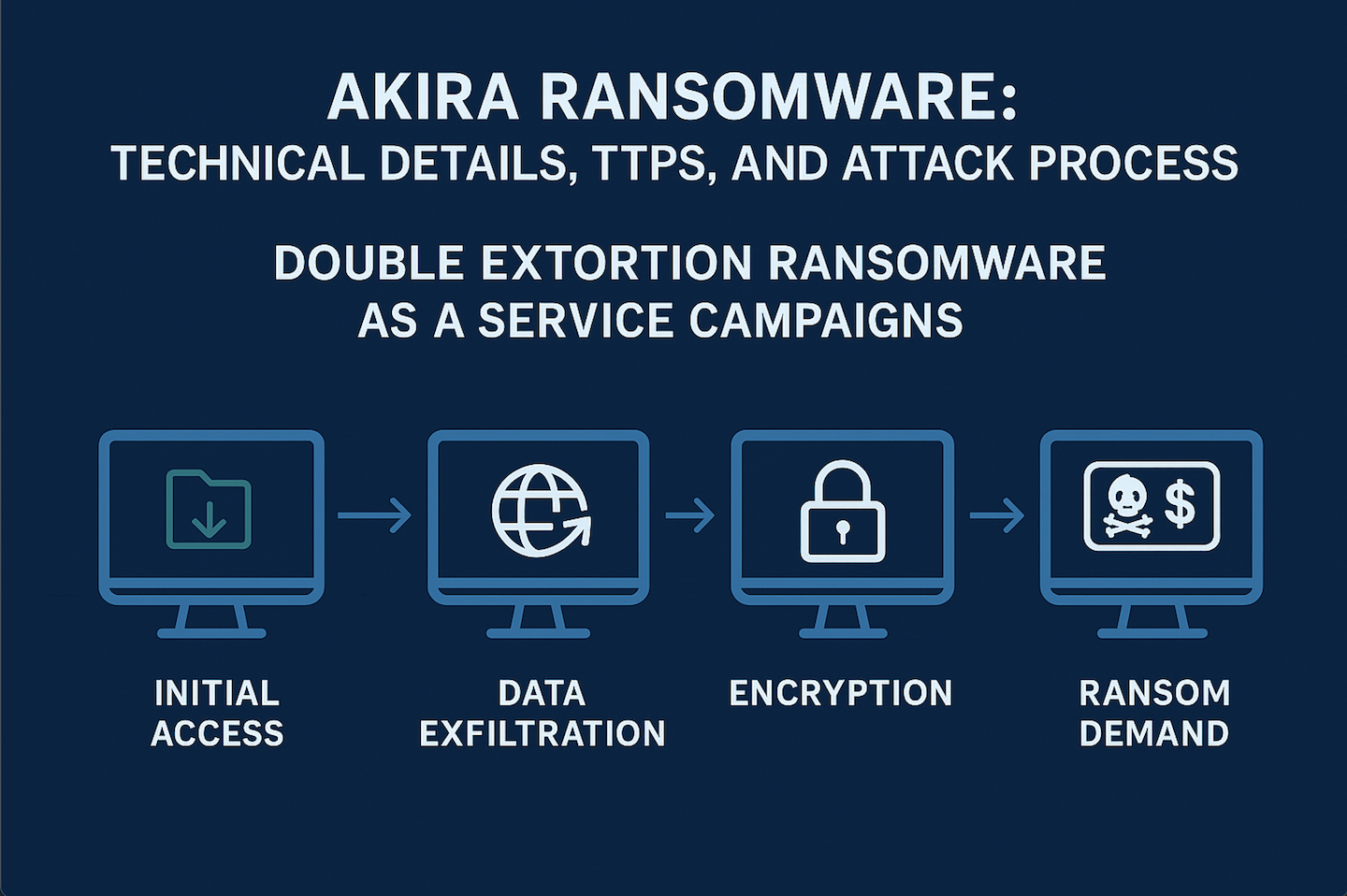
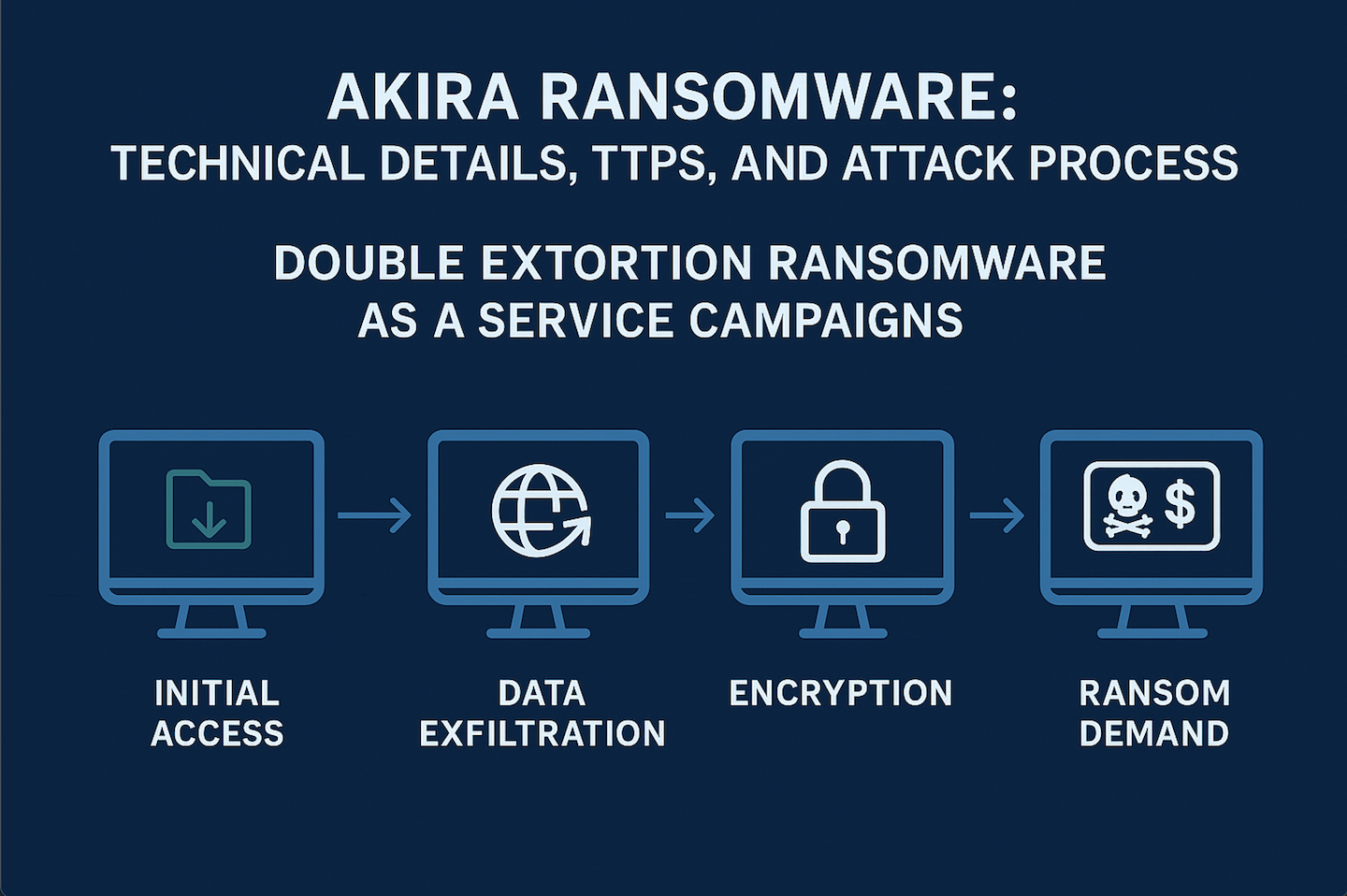
Akira Ransomware: Technical Details, TTPs and Attack Process

.
February 10, 2026
Educational

When to Pay (or Not): Ethics, Law & Strategy of Ransom Decisions

.
February 10, 2026
Educational

AI Enabled Social Engineering: The AI Blueprint for Investigators

.
February 10, 2026
Product

AiiR-As-A-Service: Always-On Breach Response for a New Era

.
February 10, 2026
Educational
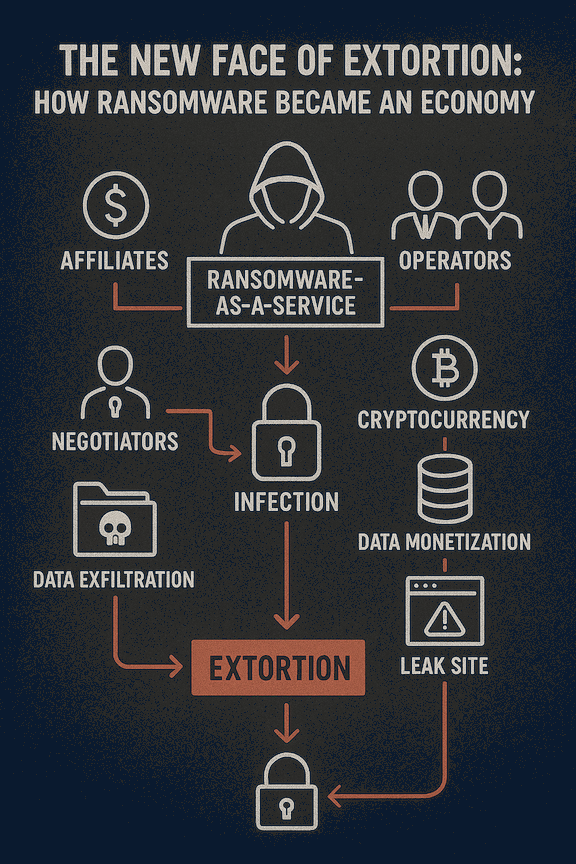
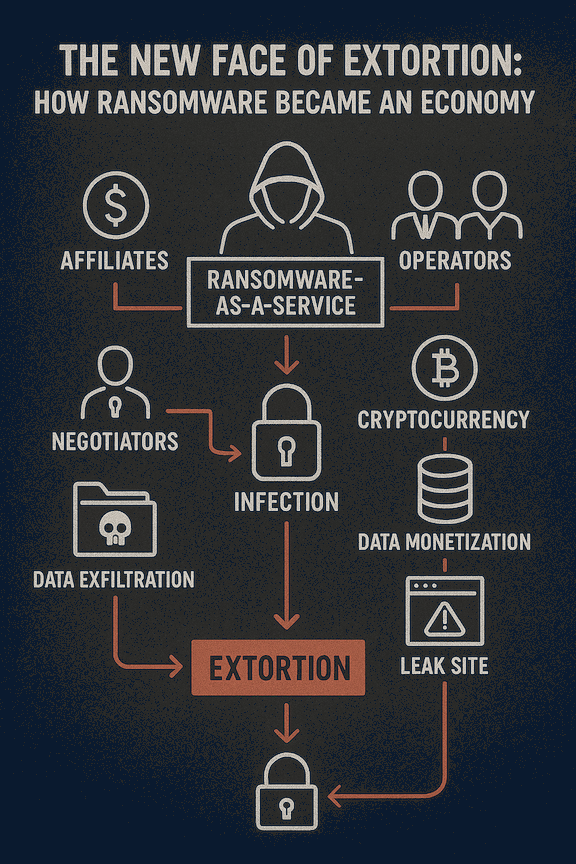
The New Face of Extortion: How Ransomware Became an Economy

.
February 10, 2026
Product
Why run AI Driven Ransomware Tabletops

.
February 10, 2026
.svg)




.svg)