.svg)

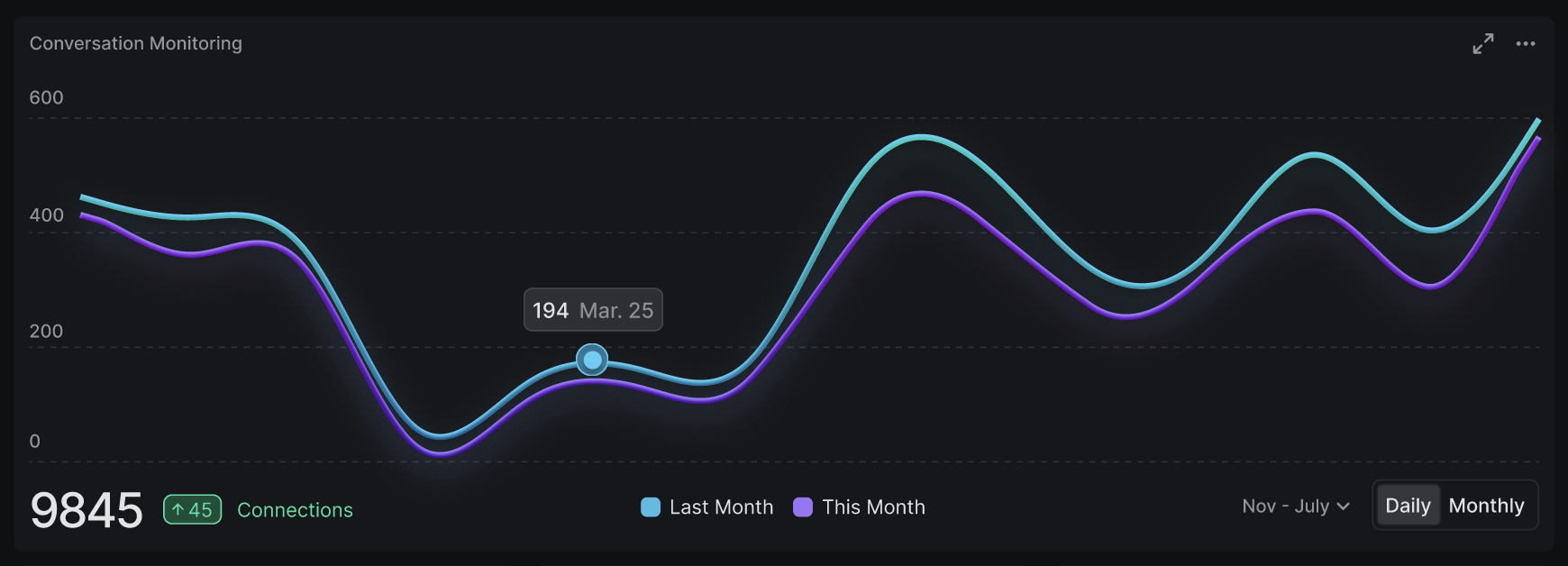
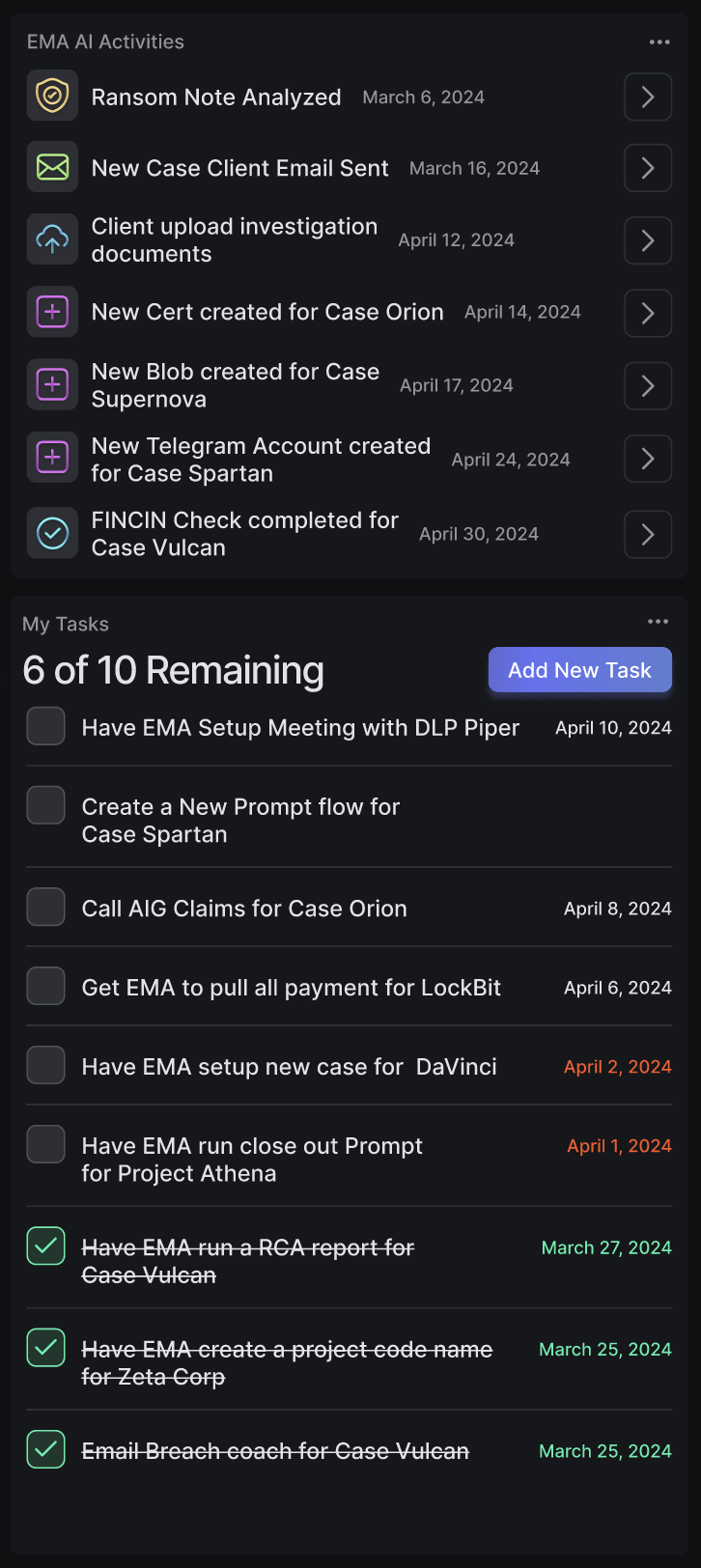
A unified dashboard to track negotiations, monitor threats, and streamline breach response in real time.

.svg)


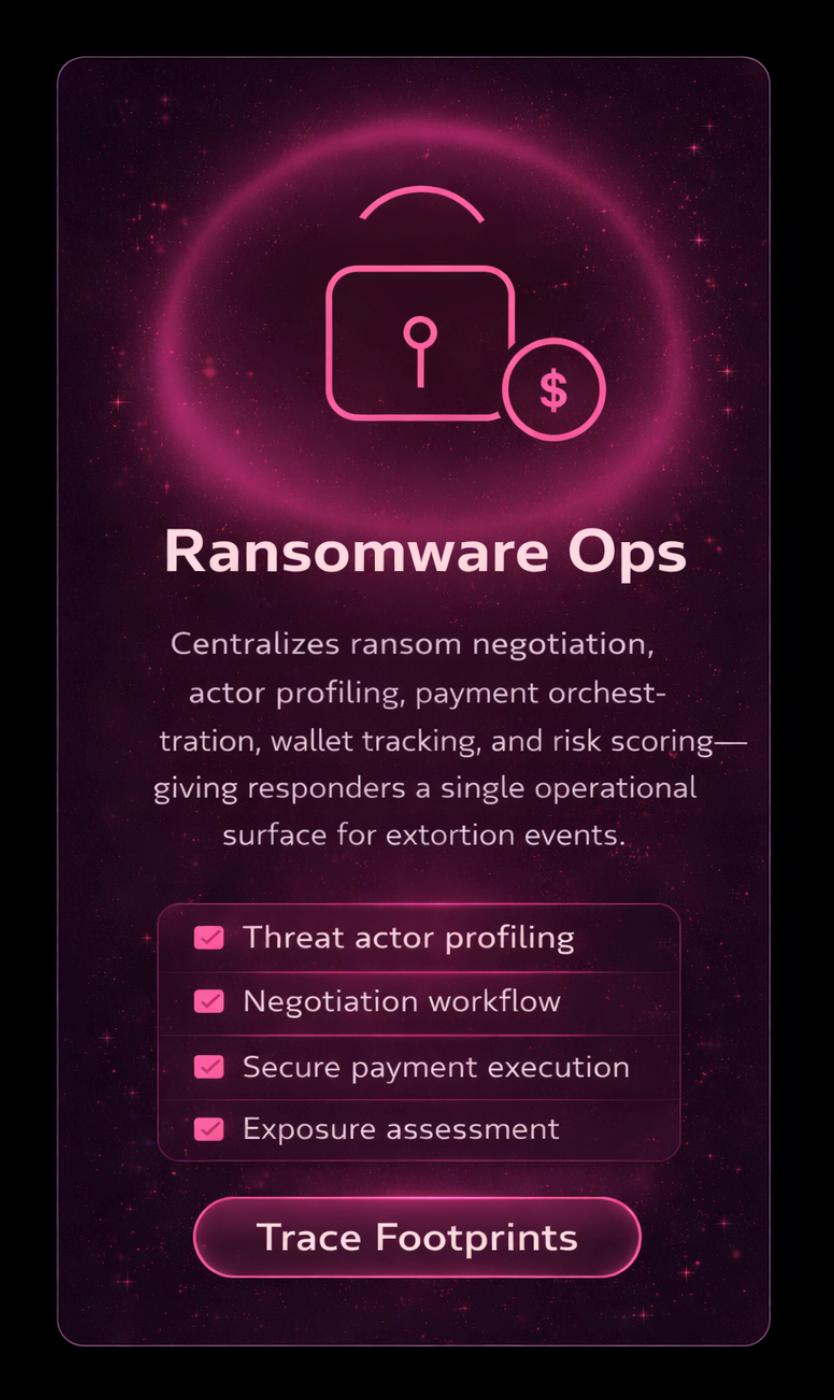
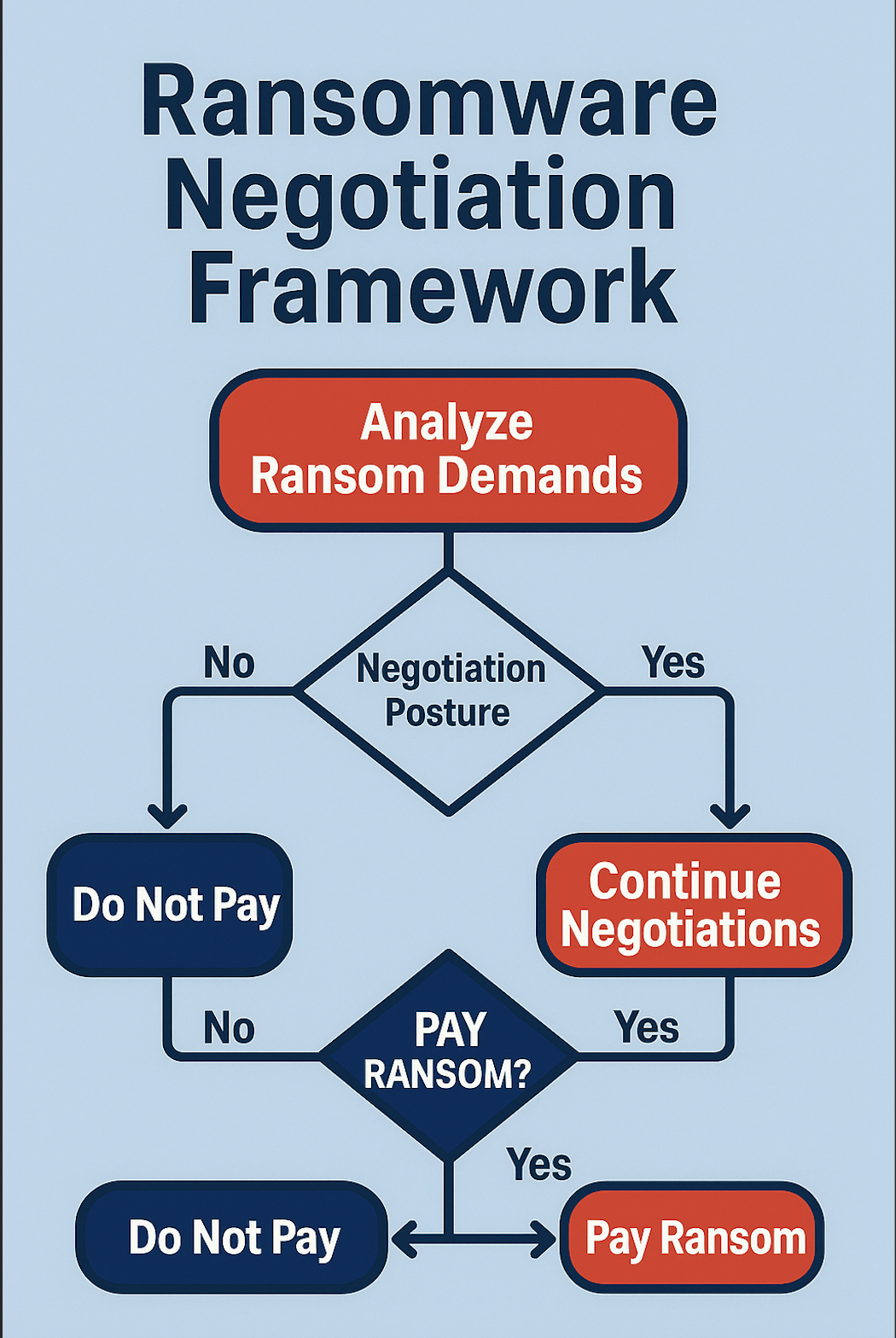
Ransomeware & Extortion
CEIRA launches negotiation agents, analyzes ransom notes, tracks wallets, builds negotiation strategy, and coordinates containment — while generating regulator-ready evidence in parallel.
Agents execute:
- Ransom analysis + strategy
- generation Wallet intelligence + payment orchestration
- Evidence capture
- Containment coordination
Business Email Compromise
CEIRA analyzes mailbox activity, extracts indicators, traces fraud paths,and prepares legal documentation automatically.
Agents execute:
- Mailbox forensics
- IOC extraction
- Fraud tracing
- Legal-ready case artifacts
Nation-State / Espionage
CEIRA activates advanced hunts, maps attacker behavior to MITRE, andexports forensic + compliance packages.
Agents execute:
- Threat hunting
- MITRE ATT&CK mapping
- Forensic workflows
- Compliance exports
Accidental Data Exposure
CEIRA determines scope, validates exposure, prepares notifications, andguides remediation actions.
Agents execute:
- Exposure assessment
- Impact analysis
- Notification readiness
- Remediation guidance
Insider Threat / IP Theft
CEIRA reconstructs identity activity timelines, builds evidence chains,and prepares HR/legal handoffs.
Agents execute:
- Identity activity review
- Timeline reconstruction
- Evidence packaging
- HR/legalworkflows
Payment Fraud / HR Investigations
CEIRA traces financial activity, organizes case notebooks, and generates reporting artifacts.
Agents execute:
- Financial tracing
- Structured case documentation
- Executive reporting
.svg)
.svg)
















.svg)