What Are Dark Web Leak Sites?
Leak sites are websites maintained by ransomware groups to publish stolen data from victims who refuse to pay a ransom. These sites are often hosted on the Tor network to evade takedown and detection.
Key characteristics:
- Publicly accessible via Tor
- Frequently updated with new victims
- Often include countdown timers, proof-of-life samples, and searchable databases
These sites aren’t just tools of exposure—they’re psychological weapons.
The Role of Leak Sites in Ransomware Campaigns
Leak sites serve several strategic purposes for threat actors:
- Pressure Tool: Threaten public embarrassment or legal scrutiny to push for payment
- Proof of Breach: Show credibility with preview data
- Affiliate Incentive: Drive competition among ransomware-as-a-service (RaaS) affiliates
- Searchable Index: Allow journalists, regulators, and competitors to find exposed data
Leak site announcements often signal that the group believes negotiations have stalled or failed.
Common Features on Leak Sites
- Victim Logos & Names: To maximize visibility and reputational damage
- Data Samples: Files like contracts, HR records, PII, or emails
- Download Links: For full breach dumps, usually encrypted
- Countdown Clocks: Warning of full release if ransom isn’t paid
Why This Matters for Your Organization
Even if your systems are restored from backup, a data leak can:
- Trigger regulatory fines (e.g., GDPR, HIPAA, CPRA)
- Spark lawsuits from customers or employees
- Lead to media exposure and reputational harm
- Result in credential stuffing or insider threats
The New Reality: Extortion Without Encryption
Some modern threat groups skip the encryption entirely and rely solely on data exfiltration and leak threats. This makes traditional incident response playbooks (which focus on recovery) insufficient.
What You Can Do
- Monitor Leak Sites: Use threat intelligence tools to identify exposure quickly
- Practice Tabletop Exercises: Include scenarios where data is posted on a leak site
- Update Legal and PR Plans: Prepare breach communications and regulatory reporting workflows
- Track Stolen Data: Know what was taken and who might be affected
- Stay Ahead of Disclosure: Transparency matters—don’t let criminals control the narrative
How AiiR Helps You Fight Back
AiiR (AI Incident Response) is designed specifically to address modern extortion tactics, including those involving dark web leak sites. Here’s how AiiR equips your organization:
🔍 Real-Time Dark Web Monitoring
AiiR CEIRA AI continuously scans known and emerging ransomware leak sites on the dark web and surfaces any mentions of your organization, affiliates, or leaked assets using advanced AI and pattern matching.
🤖 EMA AI: Extortion Management Analyst
CEIRA AI (Counter Extortion Incident Response Analyst) assists breach coaches, counsel, and IR teams by:
- Automating leak site investigation and snapshot collection
- Identifying threat actor groups and known TTPs
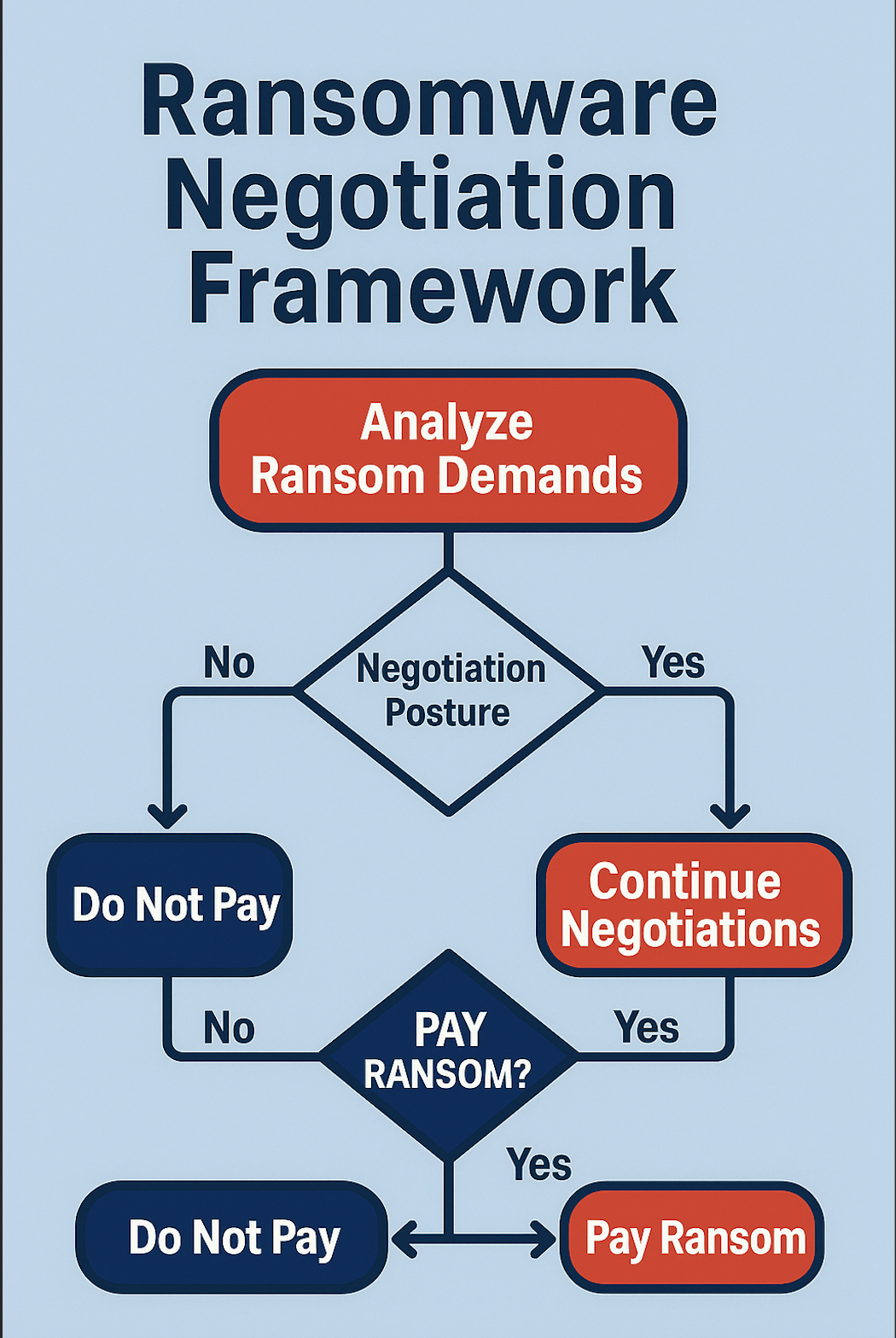
- Performs the Extortion negotiations workflows with timeline tracking and AI-generated draft responses
- Create and tracks crypto payment for threat actors
- Manages compliances across all channels FINCEN/ OFAC and other checks
- Alerting legal/comms teams with customizable playbooks
- Automate and performs AI driven tabletop exercises
🧠 Threat Intelligence & Actor Attribution
AiiR’s integrated threat intel engine maps leaked samples to MITRE ATT&CK techniques, identifies the most likely actors based on artifacts, and flags related breaches or leak campaigns—giving you strategic insight before the breach spreads.
📢 Controlled Disclosure & Notification Workflows
BreNa AI (Breach Notification & Analytics) helps your organization prepare and deploy breach notification language, generate required regulatory filings (e.g., SEC, GDPR, CCPA), and coordinate communication with PR teams to own the narrative—before the attackers do.
🛡️ Always-On Incident Response
With AiiR-as-a-Service, even small and mid-market companies get access to a “virtual retainer” of breach support, ensuring you’re never caught unprepared. No more scrambling to engage vendors mid-breach.
Final Thoughts
Leak sites represent a new frontier in ransomware strategy. They amplify the impact of a breach well beyond the technical realm, turning cybercrime into a crisis of trust and reputation. Understanding their function is key—but preparing with platforms like AiiR is how you win the response.
💡 Want a demo of how AiiR tracks, analyzes, and responds to leak site threats?
Visit www.aiiresponse.com or email us at info@GoAiiR.com.

.svg)
.svg)