Phase I: Initial Contact & Proof of Life
Goal: Establish presence, control the tone, and verify the threat.
Threat actors typically deliver ransom notes via desktop lockers or data leak site links. They may offer a small sample of exfiltrated data as "proof of life."
AiiR Advantage: EMA AI auto-reads ransom notes, analyzes threat actor language, and determines whether the note matches a known RaaS signature. (Extortion Management Analyst)
Phase II: Assessment, De-escalation & Delay Tactics
Goal: Buy time while internal teams assess damage, contact legal, and prepare strategy.
Here, language must be non-committal but respectful. AiiR's extortion negotiation AI (EMA) helps by generating responses that signal engagement but stall commitment—giving your team breathing room.
AiiR Insight: Sentiment analysis and timing patterns reveal if the actor is a bot or a human negotiator. EMA AI adjusts tone accordingly.
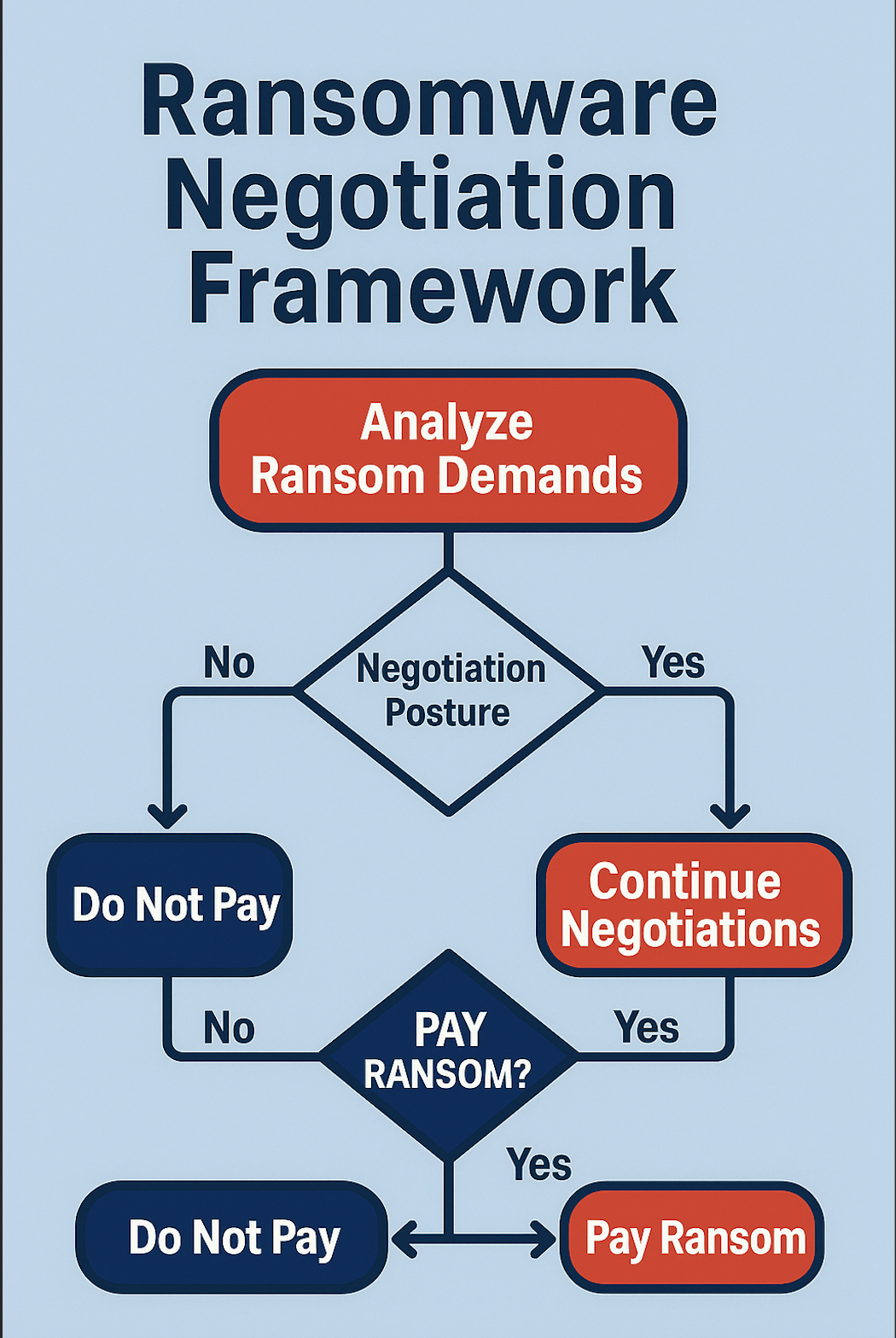
Phase III: Counteroffers & Psychological Maneuvering
Goal: Reduce the ransom demand, test flexibility, and gather intelligence.
Threat actors expect negotiation. They'll often start high. Here, psychological tactics matter—pleas of poverty, feigned internal chaos, or comparative counterexamples can shift outcomes.
AiiR Support: EMA AI offers historical price benchmarking based on threat actor profiles and previous interactions, supporting better counteroffer framing.
Phase IV: Closure, Payment Logistics & Reassurance Loop
Goal: Settle, ensure data return/deletion, and confirm no future attacks.
Crypto payments require technical execution, regulatory navigation, and chain tracing. AiiR integrates with Coinbase and forensic wallets for secure and traceable payments.
AiiR Closure: EMA AI logs all communication and flags language used by actors in post-payment attacks, helping build a long-term defense profile.
Bringing It All Together
Ransomware negotiations follow a rhythm—threat actors rely on it. The best defense? Know the phases. Anticipate the moves. Let AI orchestrate the play.

.svg)
.svg)