The Illusion of Anonymity
Many attackers still rely on Bitcoin, Monero, and Ethereum to move ransoms through wallets, tumblers, and exchanges. But public ledgers mean that, unlike traditional banking, every transaction is logged and traceable.
What once felt like digital invisibility is now a trail of clues.
How Blockchain Forensics Works
Blockchain forensics tools analyze wallet transactions, cluster addresses, identify patterns, and cross-reference known threat actor wallets. These tools link:
- Ransom payments to past breaches
- Exchange usage to real-world identities
- New wallets to previously sanctioned entities
AiiR in Action: Real-Time Crypto Intelligence
With AiiR, crypto tracing isn’t reactive—it’s embedded in the negotiation process:
- Coinbase integration allows secure execution of payments
- OFAC screening protects against sanctioned wallet transfers
- Chain analysis confirms delivery, timing, and reuse of wallet addresses
- Threat actor wallet profiling flags suspicious reuse or layering behavior
The Power of Payment Intelligence
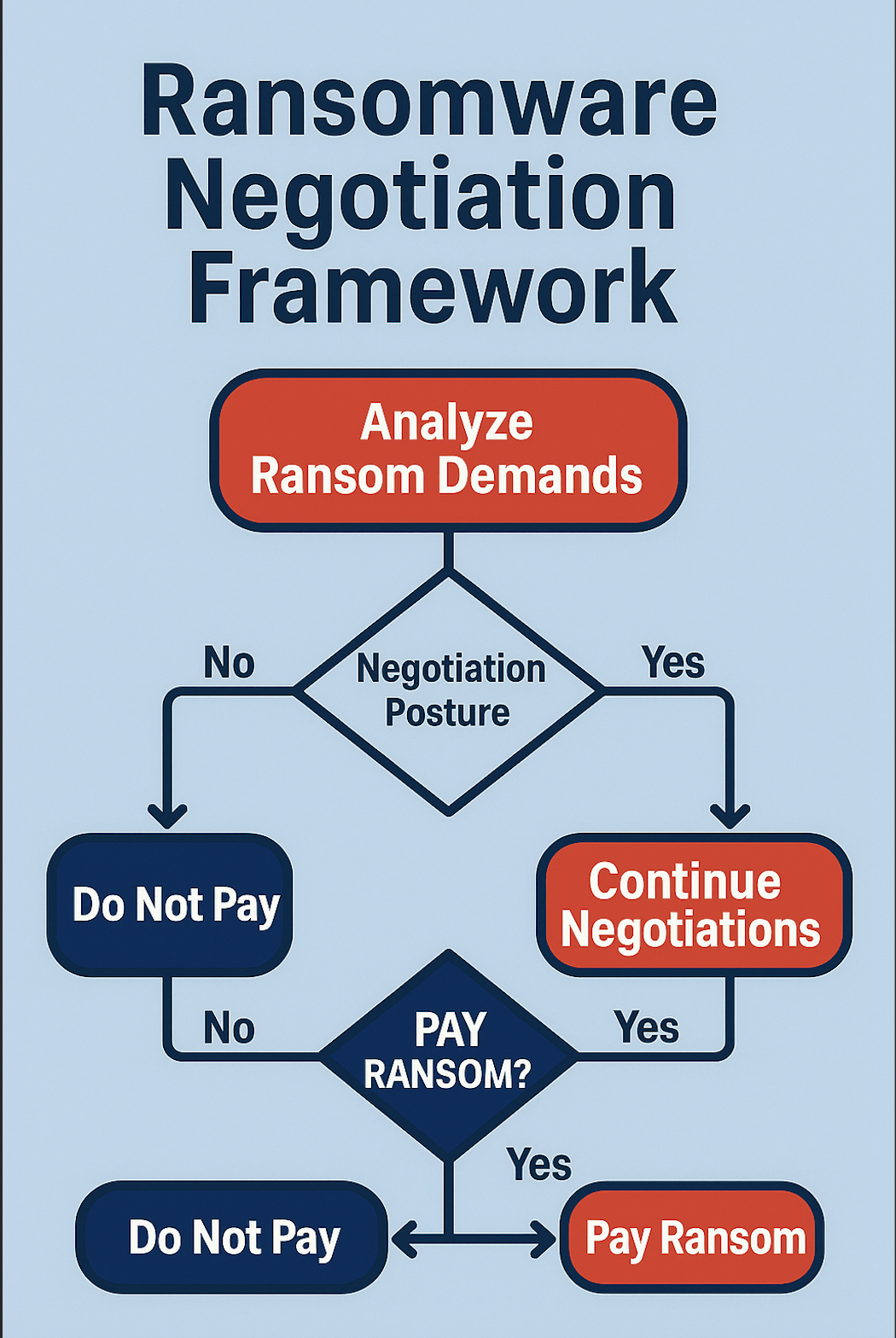
Knowing how and where the money moves changes the rules:
- Leverage: Victims can delay payment by questioning wallet legitimacy
- Intelligence: Profiling wallets gives insight into whether a threat actor follows through
- Compliance: Ensures SAR filings and FinCEN triggers are accurate and timely
Case Snapshot: Weaponizing the Ledger
In one high-profile case, CEIRA flagged a reused Monero address tied to a known RaaS affiliate. The platform recommended delaying payment, and within hours, a different wallet was offered—exposing a laundering attempt mid-negotiation.
What to Look for in Crypto Tracking Tools
- Chain support (Bitcoin, Ethereum, Monero, etc.)
- Realtime flagging of suspicious wallet activity
- Identity clustering across aliases
- Integration with OFAC/AML databases
Final Thoughts
Crypto doesn’t have to be the attacker’s edge. With platforms like AiiR, it becomes yours. Every transaction tells a story—if you know how to read the chain.

.svg)
.svg)