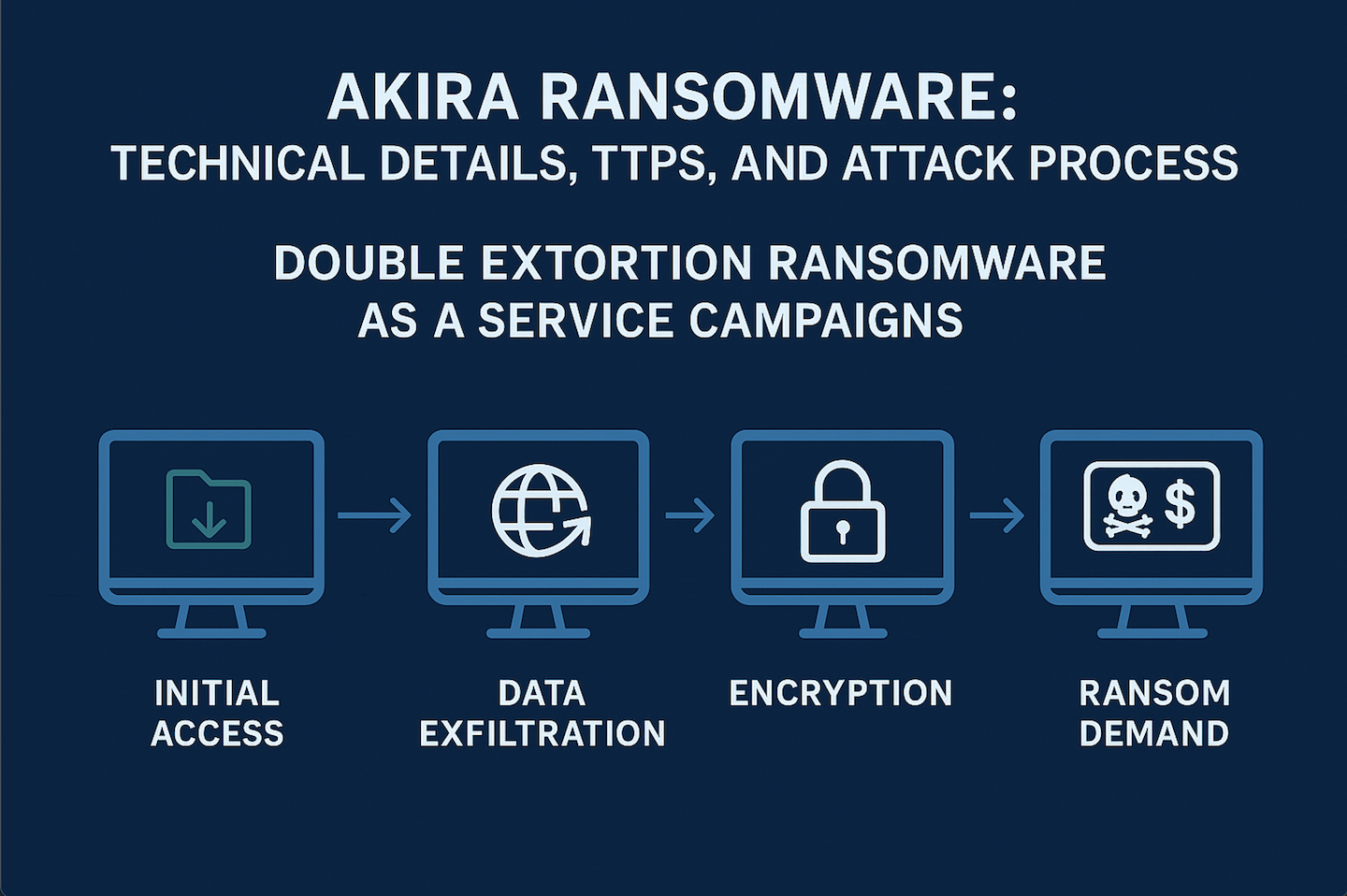
Technical breakdown of the Akira Kill Chain.
1. Initial access
Akira affiliates use multiple entry points:
- Exploiting VPN devices and public‑facing services. Akira actors gaining access via virtual‑private‑network services that lacked multi‑factor authentication, often abusing known Cisco VPN vulnerabilities (CVE‑2020‑3259 and CVE‑2023‑20269). They also exploit other externally facing services such as RDP and conduct spear‑phishing.
2. Post‑exploitation and lateral movement
Once inside, Akira operators conduct reconnaissance and move laterally:
- Persistence via new domain accounts. Investigations show Akira operators create new domain accounts (e.g., itadm) to maintain persistence.
- Discovery and credential harvesting. The actors enumerate Active Directory using tools and commands such as Get‑ADUser, Get‑ADComputer, AdFind, SoftPerfect Network Scanner, PCHunter, Advanced IP Scanner,SharpHound, MASScan and reconftw. They extract credentials by dumping LSASS memory and using Mimikatz and LaZagne.
- Lateral movement. Valid accounts and RDP are used to spread across the network. Tools like PsExec facilitate remote command execution, while the actors abuse scheduled tasks and new accounts for persistence.
3. Command‑and‑control and defense evasion
Akira affiliates rely on commodity tools for command‑and‑control and stealth:
- Remote access software. Here is a list of tools used to maintain footholds and move data, including AnyDesk, MobaXterm, Ngrok, Cloudflare Tunnel, Radmin, NetCat and RustDesk. SystemBC is another tool observed for C2.
- Disabling security products. Akira actors have been seen using tools like PowerTool to exploit a driver vulnerability (BYOVD) and terminate anti‑virus processes. They modify registry values (e.g., DisableRestrictedAdmin and user‑list keys) to hide new accounts and reduce logging.
4. Data exfiltration and impact
Before running the encryptor, the attackers exfiltrate sensitive data:
- Collection and archiving. Akira operators gather files, archive them using WinRAR, 7‑Zip or built‑in scripts, and transfer the archives off‑site. Tools such as FileZilla, WinSCP and Rclone are used to move data via FTP/SFTP or cloud‑storage services.
- Double extortion. After exfiltration, the group encrypts the victim’s environment and posts proof of the breach on their leak site. They do not provide a ransom demand in the initial note; instead, victims receive a unique code and must log in to the actors’ chat portal on Tor to negotiate.
5. Encryption process
The encryptor uses a hybrid scheme and offers granular control:
- Hybrid encryption. Akira’s Windows encryptor combines the ChaCha20 stream cipher with an RSA public‑key system, enabling fast encryption and secure key exchange. Encrypted files are appended with akira or powerranges extensions and a ransom note (fn.txt) is left in each directory.
- Command‑line arguments. Sample analysis reveals that Akira’s binary accepts parameters such as --encryption_path (-p), --share_file (-s), --encryption_percent (-n), -localonly, --exclude (-e) and -l for logging. These options allow affiliates to define which directories or network shares are encrypted, the percentage of each file to encrypt and whether to skip network drives.
- Preparation steps. Prior to encryption, the malware enumerates running processes using the Windows Restart Manager API to safely close files. It deletes Volume Shadow Copies by running powershell.exe -Command “Get‑WmiObject Win32_Shadowcopy | Remove‑WmiObject” and may remove Veeam backups and other recovery mechanisms.
- ESXi variant. Akira has developed an ESXi encryptor (Akira_v2) for VMware hosts, in addition to the Windows‐specific “Megazord” variant.
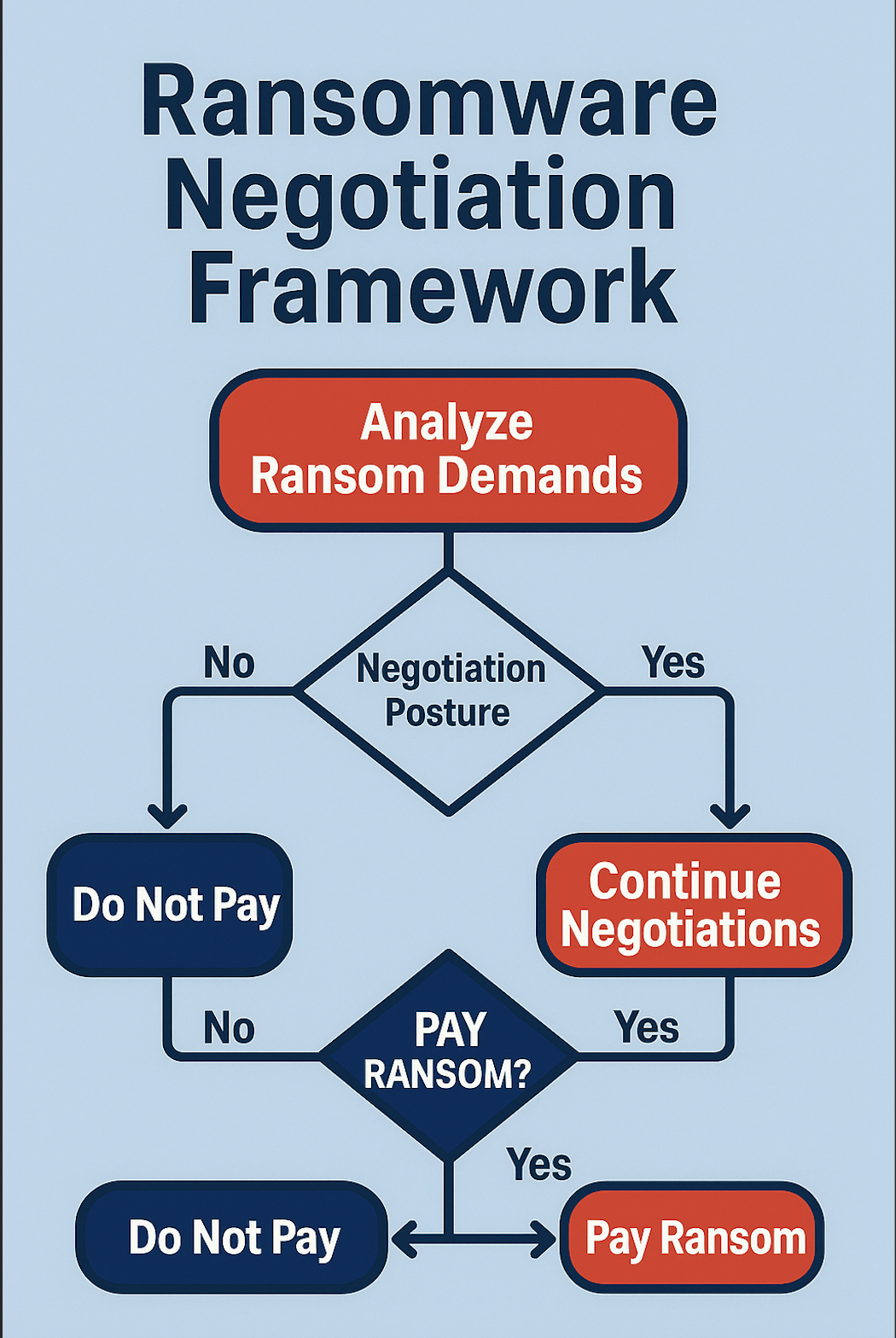
6. Ransom demand and negotiation
Akira follows a professionalized negotiation model:
- Victims are instructed to contact the attackers via a Tor‑based chat portal using a code in the ransom note. The actors typically demand payment in Bitcoin and threaten to publish data if negotiations fail. In some cases, they phone victims to increase pressure.
Defensive considerations
To defend against Akira, Organizations need to remediate known exploited vulnerabilities, enable multifactor authentication on all remote services, patch software promptly and conduct regular vulnerability assessments. Additional mitigations include monitoring for unauthorized user creation, disabling unused VPN services, segmenting networks and educating employees on spear‑phishing and credential‑theft tactics.

.svg)
.svg)