The New Face of Extortion: How Ransomware Became an Economy
The rise of digital extortion is no longer just a technical problem. It’s an economic machine. Welcome to the new ransomware economy.
The Industrialization of Ransomware
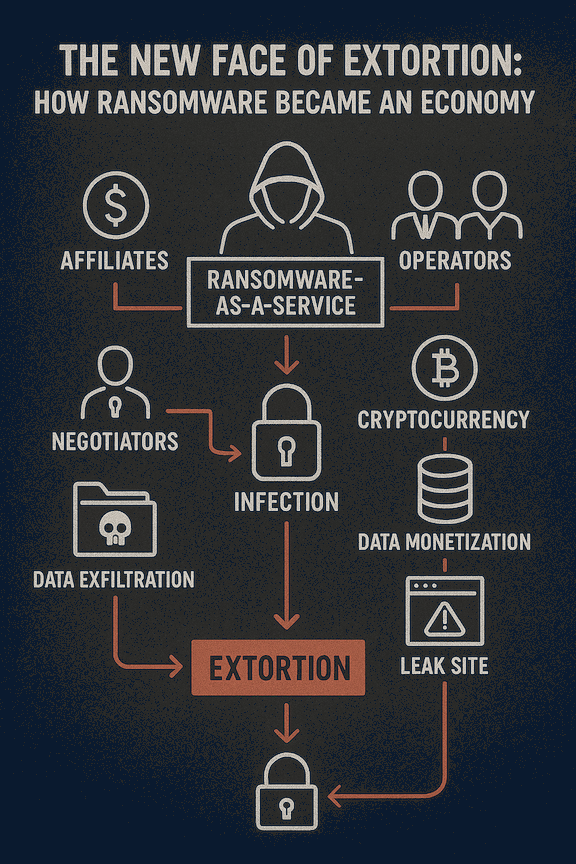
Over the past five years, ransomware has evolved from a lone wolf hacker scheme into a full-blown industrialized operation. Today, it mirrors the structure of a legitimate business: affiliates, support desks, pricing calculators, marketing teams (on the dark web), and even customer service. This is the world of Ransomware-as-a-Service (RaaS).
These operations allow even low-skilled threat actors to launch sophisticated attacks by subscribing to RaaS platforms. The result? A boom in ransomware incidents, driving billions in illicit revenue annually.
What Drives the Ransomware Economy?
Several key forces are propelling the growth of the extortion market:
- Cryptocurrency: Pseudonymous payments make it easy to transfer funds across borders without detection.
- Data Monetization: Stolen data has multiple value layers—extortion, resale, identity theft.
- Leak Sites: Public shame is now a weapon. Victims face pressure not just from encryption, but from exposure.
- Insurance: Some cyber insurance policies historically covered ransom payments, making it a viable path for fast resolution.
Meet the New Threat Actor
Modern ransomware actors aren't lone hackers. They are:
- Affiliates: Contractors using ransomware kits to launch attacks and share profits.
- Operators: Core groups managing infrastructure, payloads, and negotiations.
- Negotiators: Specialized team members who handle victim communication.
- AI Augmentation: Some threat groups are now using language models to draft negotiation messages, conduct sentiment analysis, and stage psychological pressure tactics.
Extortion, Not Just Encryption
Today's attacks rarely rely on just locking files. Double and triple extortion models have become standard:
- Encrypt data
- Exfiltrate sensitive files
- Threaten public leaks or contact your customers/regulators
The goal is not disruption. It's leverage.
How AiiR Fits In
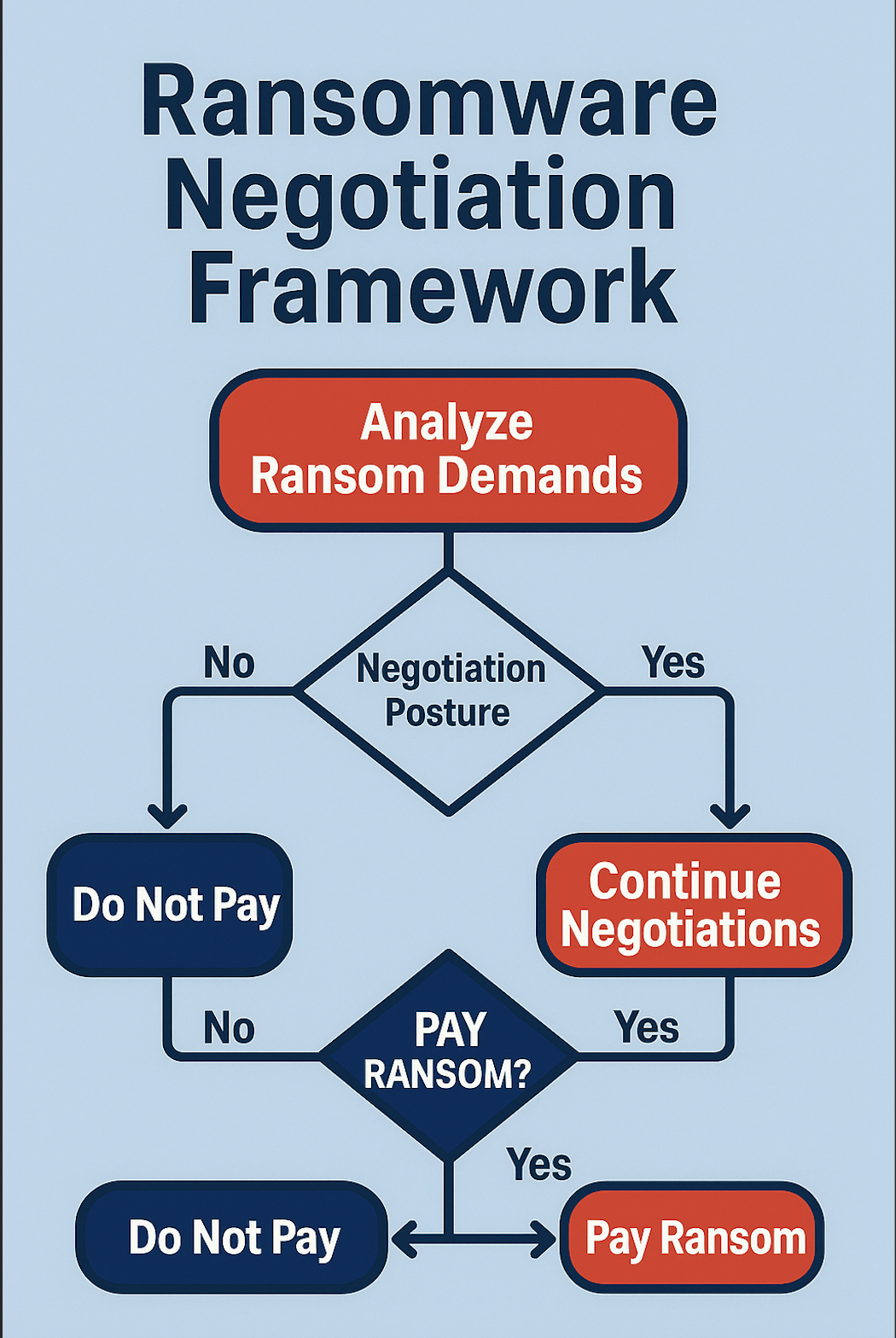
The AiiR platform was purpose-built for this new reality. With CEIRA—the Counter Extortion Incident Response AI—it helps breach coaches and security teams respond with speed, intelligence, and control.
- Profile threat actors and identify RaaS tools
- Automate early negotiation responses
- Coordinate secure crypto payments
- Integrate with blockchain forensic tools
Ransomware isn’t going away. But how we respond can evolve.

.svg)
.svg)